Building secure WordPress websites
Written by on March 5, 2021
Security is super important and if you read on the internet about creating secure WordPress websites you will get conflicting advice. In this post I will explain what we do at Highrise Digital to make the websites we build as secure as we can and the rationale behind that.

Security is everyone’s responsibility
Security can never be the sole responsibility of one person or organization. Instead it must be a collective effort, perhaps led by someone specific in an organization but everyone must be responsible.
Security is never just one thing that makes your site secure and as a result there are many protections taking place at the same time. As a result, if one of these is breached then it compromises the security of the whole system. For that reason it is vital that everyone plays their part.
Security is never done
I hear so often, particularly in the WordPress space that they are secure because they have installed a security plugin, or because their site is hosted in a particular host which is super secure.
The truth is that security is a constant ongoing effort to make sure that your website is as secure as it can be. It is never done.
WordPress website security at Highrise Digital
So, what do we do at Highrise Digital to build WordPress websites that are as secure as possible?
As I have already mentioned, security is not just one thing and therefore I am going to outline the measures we take.
Passwords and authentication
1. Strong, long passwords
Password length is the number 1 way in which you can make your passwords more secure. This is because the longer a password becomes, the harder it is to guess the password by what we call brute force attempts.
This is where a computer will constantly try different combinations of passwords to try and guess the correct one.
All passwords are a combination of known letters, numbers and symbols and therefore all a computer has to do to guess your password is try every possible combination before it will eventually find the right one.

If your password is, for example, 1 character long of letters A – Z, your password will be guessed in at most 26 attempts. Adding length and then numbers and symbols as well as upper and lower case letters to that immediately makes it harder, or more important it takes longer to guess.
Now, you might be saying “Mark, but I can’t remember longer passwords?”, and to that I would say good!
To solve that problem, we always use a password manager. A password manager is a small piece of software that stores all your passwords in a secure, encrypted vault. You have 1 password to unlock the vault (which should be super long of course) and then this gives you access to all your passwords. This means your passwords for everything can be super long.
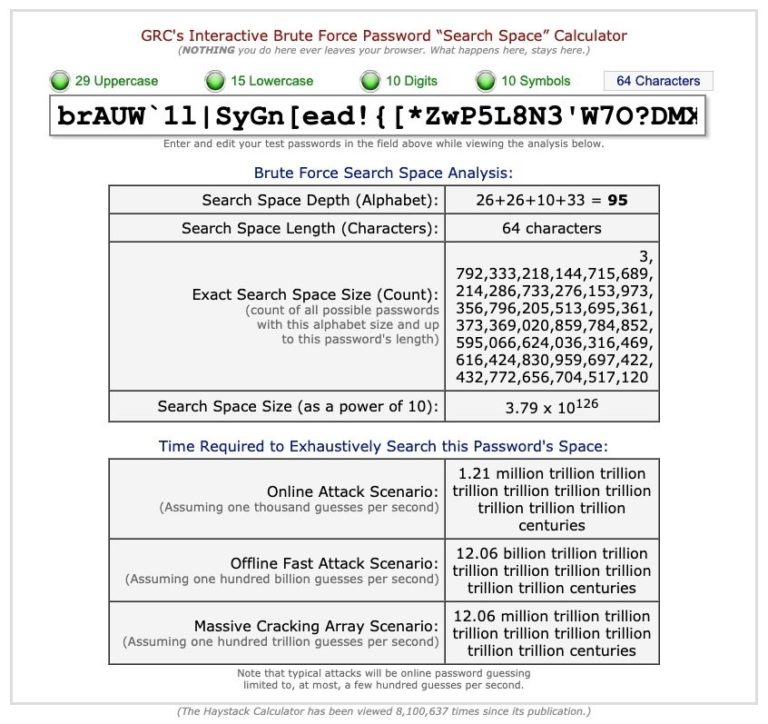
In fact, the longer the better. All our passwords for any account we create (which doesn’t limit the password length) are 64 characters long and a mix of upper and lower case letters, numbers and symbols. As you can see from the image above, the probably of that being guessed is quite low.
Link: https://www.grc.com/haystack.htm
Passwords in WordPress
It might be harder than you think to get your clients using a password manager and many of them are paid for products. If you are interested we use 1Password.
However, WordPress has its own built in password strength metre that gives users an idea of the strength of the password they are entering. Additionally when a user uses the password reset option, WordPress provides a suggested, strong password.
Finally, there are some WordPress plugins to help users force themselves to have a strong password. A WordPress strong password plugin query will find a number of plugins.
We don’t use these plugins, mainly because of the next point below!
2. Two-factor authentication (2FA)
You may have heard of two-factor authentication, often referred to as 2FA. It is a very important part of creating a secure website.
2FA is based on the principle of something you know (your password) and something you have (a 2FA code).
This means that when you login to your site, as well as being asked for your username and password, you will also be asked for a code that has been sent, usually to your phone.
If someone does crack your password, they would then need this code in order to access your site, meaning they would also need to steal your actual phone.
If you use online banking, you will already use 2FA, often with a card reader where you enter your credit/debit card and then enter your pin which provides you with a 2FA code or perhaps through your banking app on your phone.
The good news is that WordPress makes it super easy to add 2FA to your site, using the featured plugin called “Two-factor”. The plugin is really easy to set up and provides many options for using Two-factor authentication.
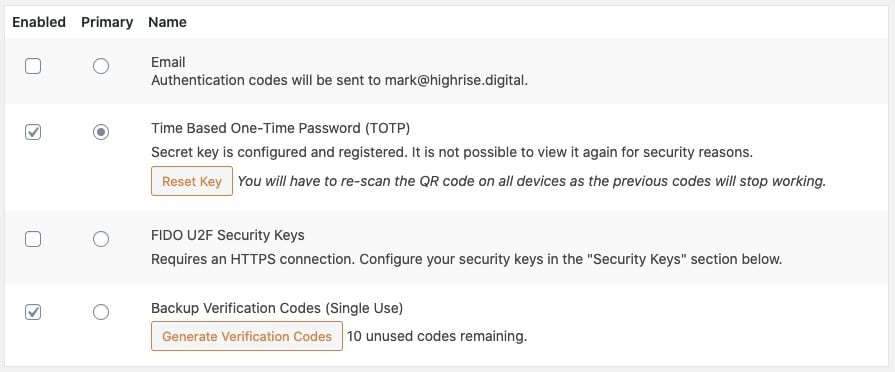
There is the option of WordPress simply sending an email to a user when they login which will contain the 2FA code. Users can also select to use an authenticator app such as Google Authenticator or you can use the 2FA field built into many password managers.
Poor password strength and the lack of 2FA are probably the largest vectors through which sites get attacked.
3. DO NOT share passwords
This sounds obvious but I see it done so many times! You mention to a client that you will need to login to their hosting and then they immediately provide you with their username and password in an email!!
This is bad for 2 reasons. Firstly, they have provided those login details through an insecure means which means they could have been intercepted. Secondly, you are then logging into the service as that person. This means that auditing what has happened breaks down.
Usernames and passwords should belong to a person and only be used by that person. If someone else needs access then they should be provided with a new set of user credentials, which of course can then be revoked when they are no longer needed.
Secure connections
When we are working to build a WordPress website we often have to connect to a number of different services such as servers. For example, the website itself where we login to the WordPress admin and connect to the server to place files as part of the development process.
All websites that we build at Highrise Digital, are served over SSL, using the HTTPS protocol in the browser. This is where you see the little padlock symbol in your browser, meaning that all data transferred between the server and the visitor (the client) is encrypted and secure.
Similarly, when using file transfer protocols to send data to and from the server, we always use, where possible the secure versions of these protocols such as SSH (secure shell) and sFTP (secure file transfer protocol).

Keeping software up-to-date
Another super important aspect of security is making sure that you keep all your software up to date.
WordPress, like most software, gets updates every now and then. Many of these are enhancements and improvements, providing new features, but they are also for security reasons to patch issues that have been found.
It really is important to make sure that you have your software updated as soon as possible, or better still let your software auto-update.
Auto-update everything
At Highrise Digital we set all our projects to auto-update as soon as the update is available to the site. This includes WordPress core, themes and plugin updates to the site. If any of those becomes compromised and there is a security update to patch the vulnerability, an automatic update is always going to be faster than a manual one.
But what if the auto update process breaks the site?
There are very odd occasions when software updates can cause your site to have problems. Usually this is because of poorly coded plugins or themes or when themes and plugins conflict with each other because of a change in WordPress.
However, such occasions are very rare and we take the approach that for 99% of time that the updates will be fine it is better to take that approach and then deal with an issue when it arises, rather than waiting for manual updates and risk the site being compromised.
It is worth noting here that to do auto updates well, relies on a couple of other things.
The first of these is an uptime notification. We need to be notified the minute the site goes down and then action can be taken to rectify this. We use Uptime Robot for this.
Secondly, backups (see below) in order to restore the site to how it was before the problem. Once restored we can then investigate and look into the problem.
A robust and reliable backup service
Having reliable, solid site backups is a critical part of any website being secure. Should the worst happen it is super important to be able to get the site back up and running as quickly as possible and a backup is the likely source of this, most of the time.
Automate your backups
Too many opt for a manual backup which fails 100% of the time when you forget to take the backup. An automated backup service will always have you backup completed in a set routine and if for any reason this backup fails, you will be notified.
In my opinion it is always best to have the site backup at the server level, rather than using a WordPress plugin. This is because a WordPress backup plugin will only work if WordPress is able to run.
However with a server level solution, not only will it backup the site, if for example there is a reason WordPress cannot load and it will be a much quicker backup doing it at the server level.
The majority of good WordPress hosting companies will provide daily backup and restore service (at the server level) which backs up your site on a daily basis and gives you the ability to restore the site in a single click. These are the best backup facilities available.
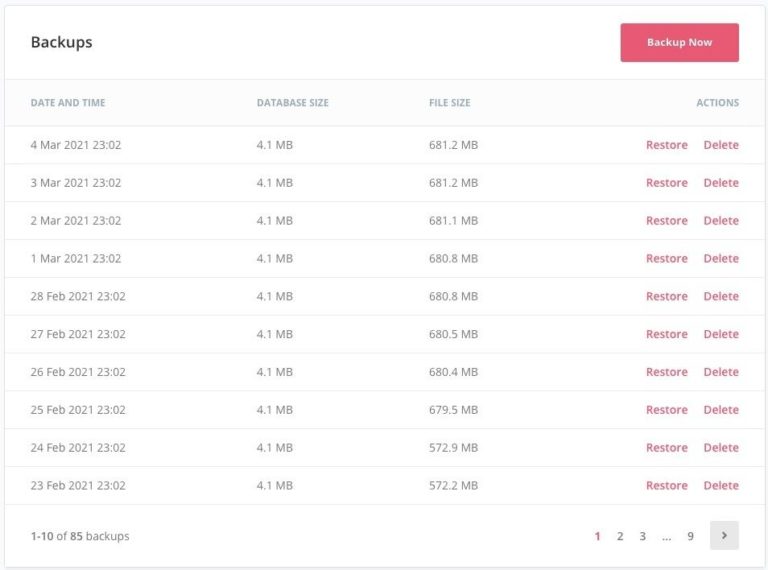
However what happens if you cannot access your host? Unlikely but not impossible. If you cannot access your host and your backups are with your host, this means that you cannot access your backups and you are in trouble.
For this reason, as well as your host providing your primary fail-safe backup, we would recommend you complete an off-site backup as a sensible interval – maybe once a week. This is where you could use a WordPress plugin such as BackupBuddy or, like us ManageWP.
Following best practice WordPress coding standards for security
When writing code in general, but also in WordPress, there are a number of principles that you should be following. For WordPress developers, we are really lucky because WordPress provides us with lots of functions that we can use in our code to make it more secure.
I can’t go through everything in this post but I am going to concentrate on 3 main things, which we do at Highrise Digital in our code to make sure that it is more secure.
Escaping Data
Escaping data is the process of securing output by stripping any unwanted data such as script tags, incorrectly formed HTML and other unwanted data. It therefore prevents this data being seen or executed as code.
I have previously written about how to escape data in WordPress, using the functions available, so do take a look at that post.
Sanitizing data
Similar to escaping is data sanitization. This means that before we save any data to the WordPress database, we need to make sure that the data is in the format we expected and does not contain anything that we didn’t expect.
Think of sanitizing data as cleaning it up or filtering it before we do anything with it.
WordPress provides a number of sanitize_() functions which we can use depending on the type of data we are storing.
You can learn more about sanitizing data in WordPress over on the WordPress developer handbook.
Making use of nonces when processing data
There are often times in WordPress when users submit data through forms. This could be on the frontend of the site or in the WordPress admin area when editing content etc.
Developers should always be checking whether the current user has the capability to carry out that action. For example, only a WordPress administrator can manage changes to a site’s options.
However, as well as checking for whether the current user is capable of carrying out a request, we also need to to check for intent – whether they actually meant to do a certain thing at a certain time. It could be that a user is tricked into doing something.
The example I often use to explain this, is a door card often used in schools and hospitals. Staff have a card which they wave at a pad on the door to open the door. The card is like the capability in WordPress, it says that this card has the capability of opening or not opening this door. However this doesn’t check for intent. If the card was stolen, someone else could still open a door, even though the owner of the card did not intend it.
To check for intent in WordPress we always use something called a NONCE. It stands for “number used once”. Nonces are added to forms, can only be used once and have a limited lifetime. Used alongside capability checks they help authorise for the user and their intent.
You can find out more about how to use nonces in WordPress on the developer handbook.
Independent security audits
When clients are concerned about security for whatever reason, we often recommend an external security audit of our work.
This is where an external, independent security consultant looks over the whole project and makes recommendations (hopefully not that many!).
What is not security?
As I mentioned at the start of this post, if you look around the web for advice on best practice for security you will get a lot of different advice. Some such advice resolves very much around what is termed security through obscurity.
This essentially means trying to secure things by hiding them. A typical example that you will find is advice about hiding the WordPress login page.
This is not a good security practice. It is akin to leaving the key under the mat or the plant pot or even painting the front door so it looks like a wall of the house. Just because something is hidden does not mean that it is secure.
Practices such as hiding the login page may have a small benefit, but I would argue they can cause more harm than good sometimes. What they are not, is security.
Summary and take-aways
Security is not something to brush under the carpet and hope that it will be dealt with by others but something that should be at the forefront of everyone’s mind when completing a project.
I hope you can see from this post that there are a series of relatively simple steps that you can take to really improve your site security, making sure you think about security from the very start.
If you are not using a password manager, then I would highly recommend that is something you action straight away as it will reduce the likelihood of your passwords being compromised.
Focus on keeping your software up to date at all times and make sure that you not only have automated backups taking place, but you test the restore process too.
At Highrise Digital we put security to the forefront of all the projects we do, with the goal of making the WordPress websites we build as secure as is reasonably possible.